API Penetration Testing Explained
API penetration testing represents an essential technique for security evaluation, focusing on detecting weaknesses within APIs. These APIs are critical elements that facilitate interactions between disparate software systems. Given their role as conduits to sensitive information and functionality, ensuring their security is of utmost importance. Through detailed simulation of cyber attacks, API penetration testing seeks to identify and address vulnerabilities preemptively, thwarting potential exploitation by malicious entities.
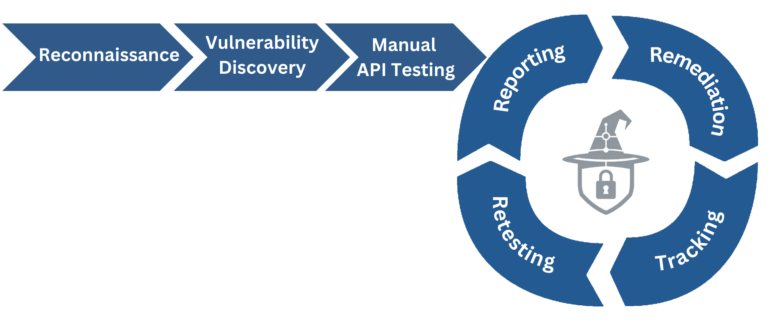
The process involves several key steps: planning, where testers define the scope and objectives; reconnaissance, to gather information about the target API; vulnerability scanning, using automated tools to identify known weaknesses; exploitation, where testers attempt to breach the API using identified vulnerabilities; and reporting, where findings are documented, including the vulnerabilities discovered, data exposed, and recommendations for remediation.
This form of testing is critical because APIs often expose more functionality than a user interface might, providing a broader attack surface. It checks for issues like broken authentication, injection flaws, improper assets management, and inadequate security configurations. By identifying and addressing these vulnerabilities, organizations can protect against data breaches, unauthorized access, and other security threats, ensuring the integrity, confidentiality, and availability of their systems and data. API penetration testing is not a one-time task but a vital component of a continuous security strategy, helping to maintain robust API security in the face of evolving cyber threats.
Reconnaissance and Business Logic Mapping
In the reconnaissance and business logic mapping phase of API penetration testing, testers focus on identifying and analyzing the web application’s API endpoints, key for accessing sensitive data and core functionalities. This critical step involves pinpointing both internal and external APIs the application uses, examining API endpoints, methods (GET, POST, PUT, DELETE), and their data exchanges. Testers either review available documentation or use tools to track API traffic for insights into their structure and operations. A crucial aspect of this phase is understanding the APIs’ authentication and access control mechanisms, including the management and potential vulnerabilities of API keys and tokens.
Automated and Manual Testing
In the Automated and Manual Testing phase of an API penetration test, testers use both automated tools and manual methods to identify vulnerabilities. Automated tools quickly scan API endpoints for common issues like injections, broken authentication, and misconfigurations, efficiently pinpointing basic weaknesses. These scans, which involve sending varied requests and analyzing the API’s responses, offer a rapid assessment of the API’s general security but primarily detect known vulnerabilities.
Contrastingly, manual testing employs a detailed, hands-on approach, crucial for finding complex vulnerabilities missed by automated scans, especially those involving business logic or sophisticated attacks. Testers manually interact with the API, carefully analyzing how it responds under various scenarios, and looking for issues such as input mishandling, authentication problems, and logical flaws. This deeper exploration, requiring both creativity and technical expertise, provides insights into more intricate security challenges. Together, automated and manual testing form a thorough evaluation process, uncovering both obvious and concealed security risks in the API.
Reporting
In the Reporting phase of an API penetration test, the focus is on compiling a comprehensive, clear report detailing all discovered vulnerabilities, their impacts, and remediation recommendations. This report categorizes the issues by severity and includes specific details such as vulnerability type, discovery methods, and supporting evidence like screenshots or logs. It serves to guide development and security teams in prioritizing and addressing security flaws effectively.
Furthermore, the report evaluates the overall security architecture of the API, offering strategic improvement suggestions on aspects like authentication, encryption, and error handling. This document is essential not only for immediate remedial action but also for long-term security planning and compliance with regulatory standards. It transforms technical findings into a strategic roadmap, equipping stakeholders with the information needed to strengthen their API’s security.
