-
Penetration Testing for Websites: Best Practices
Purpose and Importance of Penetration Testing for Websites Penetration testing for websites is a crucial aspect of…
-
Penetration Testing Services: Top 5 Benefits
Introduction to Penetration Testing Services Understanding Penetration Testing Penetration testing is like a practice drill for companies…
-
Application Security Testing: Identify and Fix Vulnerabilities
Defining Application Security Testing Checking the security of an application is really important. It helps find and…
-
Top API Security Testing Methods to Secure Your Data
The Importance of API Security Testing In today’s digital world, it’s important to keep APIs secure. APIs…
-
How External Penetration Testing help Identify Vulnerabilities
What is External Penetration Testing? External Penetration Testing is a crucial cybersecurity practice that involves simulating real-world…
-
The importance of Vulnerability Assessment in Cybersecurity
Conceptual Definition of Vulnerability Assessment In cybersecurity, vulnerability assessment is important for finding and fixing security risks…
-
Top 10 Essential Penetration Testing Tools
Understanding Penetration Testing In the world of cybersecurity, penetration testing is an important practice that helps organizations…
-
Top Security Testing Services to Secure Your Business
The Importance of Security Testing in Businesses As businesses use digital technology more and more, it’s really…
-
How to Write a Comprehensive Penetration Test Report?
What is a Penetration Test? A penetration test is a simulated cyberattack on a computer system, network,…
-
What are Essential SOC 2 Compliance Requirements?
Introduction to SOC 2 Compliance In the realm of cybersecurity, SOC 2 compliance is a crucial framework…
-
Top Web Application Penetration Testing Techniques
Definition of Web Application Penetration Testing Web Application Penetration Testing is a way to check for security…
-
Advanced Mobile Application Penetration Testing for Hidden Risks
Importance of Mobile App Security Mobile apps have become a crucial part of our everyday routines, making…
-
Why Hire a Pentest Service?
Current Threat Landscape of Pentest Services In today’s fast-paced digital world, companies are at risk of being…
-
Is penetration Testing Better than Vulnerability Scanning
Brief Insight on Cybersecurity – Penetration Testing vs Vulnerability Scanning When it comes to securing your business…
-
Top Cyber Security Testing Strategies Every Business Should Know
Why Cyber Security Testing is Important Cyber security testing is really important for businesses because it helps…
-
What is a Standard Penetration Test?
Defining Standard Penetration Testing In the realm of cybersecurity, a Standard Penetration Test (SPT) is a crucial…
-
SOC 1 vs SOC 2: Key Differences Explained for Businesses
Synopsis of SOC Reports: SOC 1 vs SOC 2 When it comes to understanding the differences between…
-
SOC2 Compliance – Why a Pentest is Crucial
Importance of SOC2 Compliance Ensuring your organization’s systems and data are secure and trustworthy is key, and…
-
Streamlining Security with Automated Penetration Testing
Understanding Penetration Testing In today’s fast-changing online world, knowing why penetration testing is important is key to…
-
Why Every Business Needs a Mobile Application Penetration Test
Importance of Mobile Applications and Mobile Application Penetration Testing in Business Mobile apps are now essential for…
-
Essential Reasons Why Web Application Penetration Testing Matters
Understanding Web Application Penetration Testing Definition and Importance of Web Application Penetration Testing Web Application Penetration Testing…
-
Why Regular Vulnerability Assessments Are Crucial for Cybersecurity
The Importance of Regular Vulnerability Assessments in Cybersecurity In today’s digital world, keeping sensitive data safe is…
-
How does our free vulnerability assessment help your security
Understanding (Free) Vulnerability Assessment It’s important to regularly check for weaknesses in your computer systems and networks…
-
Ensuring Compliance with Effective Pentest SOC 2 Strategies
Introduction to Pentest SOC 2 and its Importance Understanding SOC 2 When it comes to ensuring SOC2…
-
How Useful Is Antivirus Software in Protecting Your Digital Life?
Why is Digital Protection Important? As we use digital devices and the internet more and more in…
-
Top JWT Vulnerabilities and How to Protect Against Them
Overview of JWT and JWT Vulnerabilities JSON Web Tokens (JWT) are a common way to securely share…
-
Understanding the Risks of Storing Secrets on the Frontend Storage
Understanding The Concept of Storing Secrets On The Frontend When it comes to cybersecurity, it’s crucial to…
-
WiFi Penetration Testing: Identify Security Flaws and KRACK Risks
KRACK Attacks in WiFi Penetration Testing KRACK (Key Reinstallation Attack) is a significant cybersecurity vulnerability that targets…
-
Pentesting in Production vs Non-Production: Key Differences Explained
Understanding Penetration Testing Penetration testing is an important part of keeping your organization’s digital information safe. When…
-
Top Tips for Securing Firebase Database
Firebase Database and its Security Importance Overview of Firebase Database Firebase Database is a database tool from…
-
Exploring the Top 10 Smart Contracts Vulnerabilities
Understanding Smart Contracts Smart contracts have changed the way digital transactions work, using blockchain technology to create…
-
Understanding and Defending Against Backdoors
Backdoor Definition and Purpose In the realm of cybersecurity, a backdoors refer to a hidden method of…
-
WiFi Penetration Testing: Identify and Mitigate WPA2 Vulnerabilities
Understanding WPA2 and its Vulnerabilities When it comes to WiFi security, WPA2 has long been considered the…
-
Mobile App Penetration Testing for Secure Communication
Understanding Mobile App Penetration Testing In today’s world, mobile apps are a big part of our daily…
-
WiFi Penetration Testing: Safeguard Against Rogue Access Points
Defining WiFi Penetration Testing WiFi penetration testing, also known as WiFi pen testing, is a crucial cybersecurity…
-
Pentest Desktop Application: Protect Against DLL Injection
Understanding Pentesting of Desktop Applications In today’s world, it’s important to keep your software safe from hackers…
-
Web Application Penetration Testing for XXE Vulnerabilities
Understanding XXE Vulnerabilities XXE (XML External Entity) vulnerabilities are a common threat that can potentially compromise the…
-
WiFi Penetration Testing: How to Detect and Prevent WEP Weaknesses
Overview of WiFi Penetration Testing Testing WiFi networks for security vulnerabilities is an important part of keeping…
-
Effective Strategies for Mitigating Buffer Overflow Vulnerabilities
Understanding Buffer Overflow In the world of online security, it’s important to comprehend what we call ‘buffer…
-
Defending Against RCE: Effective Strategies
Understanding RCE Remote Code Execution (RCE) is a dangerous security threat that allows hackers to remotely run…
-
WiFi Penetration Test: Securing Against MAC Spoofing
Understanding WiFi Security When it comes to WiFi security, one of the key threats that organizations face…
-
Detecting and Preventing CSRF Attacks: A Comprehensive Guide
Understanding Web Application Penetration Testing Testing the security of your website is very important to make sure…
-
The Importance of Penetration Testing in PCI-DSS Compliance
Understanding PCI-DSS Compliance Understanding PCI-DSS compliance is essential for keeping sensitive data safe and maintaining customer trust….
-
How Parametrized Queries Protect Against SQL Injection Attacks
Understanding SQL Injection SQL injection is a common type of cyber attack where hackers exploit weaknesses in…
-
Understanding OWASP Top 10 Vulnerabilities
What is OWASP? OWASP is an organization dedicated to making software more secure. They offer resources and…
-
Understand GDPR Impact on Data Protection and Penetration Testing
Understanding GDPR and Data Protection Laws The GDPR has changed the way companies test and protect their…
-
Pentesting Your Database: NoSQL Injection Prevention
Importance of NoSQL Databases When it comes to cybersecurity, the importance of NoSQL databases cannot be overstated….
-
Penetration Testing in Agile Development Environments
Understanding Agile Development Agile development has revolutionized the way software is created and maintained in the modern…
-
Preventing Code Injection: Best Practices for Secure Coding
Understanding Code Injection Code injection is a dangerous cybersecurity threat that can cause serious harm if not…
-
How to Effectively Prepare for a Penetration Test
Understanding Penetration Testing Penetration testing is important for checking how secure a company’s systems and infrastructure are….
-
How Penetration Testing Helps Achieve GDPR Compliance
An Overview of GDPR The General Data Protection Regulation (GDPR) is a set of rules created by…
-
Master Race Condition Vulnerabilities: Causes and Solutions
Definition of Race Condition Vulnerabilities Race conditions in software happen when different parts of a program try…
-
How to Identify Phishing Emails and Avoid Scams
The Threat of Phishing Emails Phishing is a scam where cybercriminals trick people into giving away personal…
-
What is a Man-in-the-Middle Attack and How Can You Prevent It
Understanding the Need for Cybersecurity In today’s digital age, cyber criminals have found a sneaky way to…
-
How DDoS Attacks Work and How to Protect Against Them
Understanding DDoS Attacks A Distributed Denial of Service attack is a prevalent cyber threat designed to disrupt…
-
Effective Strategies to Prevent IDOR Attacks in Web Applications
Introduction to IDOR Attacks Preventing Insecure Direct Object Reference (IDOR) attacks in web applications is crucial in…
-
Defending Your Accounts from Password Brute Force Attacks
Understanding Password Brute Force Attacks In simpler terms, a password brute force attack happens when a hacker…
-
Mobile Penetration Testing: Techniques to Protect Your App
The Importance of Mobile Penetration Testing Testing the security of your mobile applications is an important step…
-
How Clickjacking Attacks Work and How to Prevent Them
Defining Clickjacking Clickjacking is a sneaky trick that cyber criminals use to make you click on things…
-
What is a SIM Swapping Attack? How to Secure Your Mobile Identity
Overview of SIM Swapping Attack A SIM swapping attack is a type of identity theft where cybercriminals…
-
Why Web Penetration Testing is Crucial for Your Website Security
What is Web Penetration Testing Website penetration testing is a way to check how secure a website…
-
What is WAF and Why Your Website Needs It
Introduction to WAF and Its Importance A Web Application Firewall (WAF) is a crucial security solution designed…
-
Red Teaming vs. Penetration Testing: Key Differences
Understanding Cybersecurity Needs When it comes to keeping your company’s online information safe, it’s important to pick…
-
Dynamic Application Security Testing for App Security
Understanding Dynamic Application Security Testing Dynamic Application Security Testing (DAST) is an important way to improve the…
-
Understanding Cyber Threat Actors: Types and Motivations
Defining Cyber Threat Actors When delving into the realm of cybersecurity, understanding the various types of cyber…
-
Essential Secure Coding Practices to Protect Your Code
The Importance of Secure Coding In today’s world of technology, it’s important for developers to use secure…
-
Understanding Red Teaming: Key Benefits for Cybersecurity
Defining Red Teaming Red teaming is an important part of cybersecurity where experts simulate cyber attacks on…
-
Essential HTTP Security Headers To Secure Your Website
What are HTTP Security Headers HTTP Security Headers are important for keeping your website safe from online…
-
What is Static Application Security Testing and Why It Matters
Overview of Static Application Security Testing Static Application Security Testing (SAST) is an important step in the…
-
From Viruses to Ransomware: What Types of Malware Exist?
Malware, short for malicious software, has come a long way since the early days of simple computer…
-
Essential Strategies to Strengthen Authentication Mechanisms
Understanding the Importance of Robust Authentication Mechanisms In the realm of cybersecurity, the importance of robust authentication…
-
How to Create Strong Passwords: Tips and Best Practices
Why Strong Passwords Are Crucial In today’s world of technology, it’s really important to have strong passwords…
-
Why Multi-Factor Authentication (MFA) Matters
Overview of Multi-Factor Authentication (MFA) Multi-Factor Authentication (MFA or 2FA) is a really important security feature that…
-
Securing Communication Channels: Tips and Best Practices
The Importance of Securing Communication Channels Securing communication channels is paramount in today’s digital landscape where cyber…
-
Strategies to Prevent Insecure Data Storage on Mobile Devices
What is Insecure Data Storage Insecure data storage means that when important information is not stored properly…
-
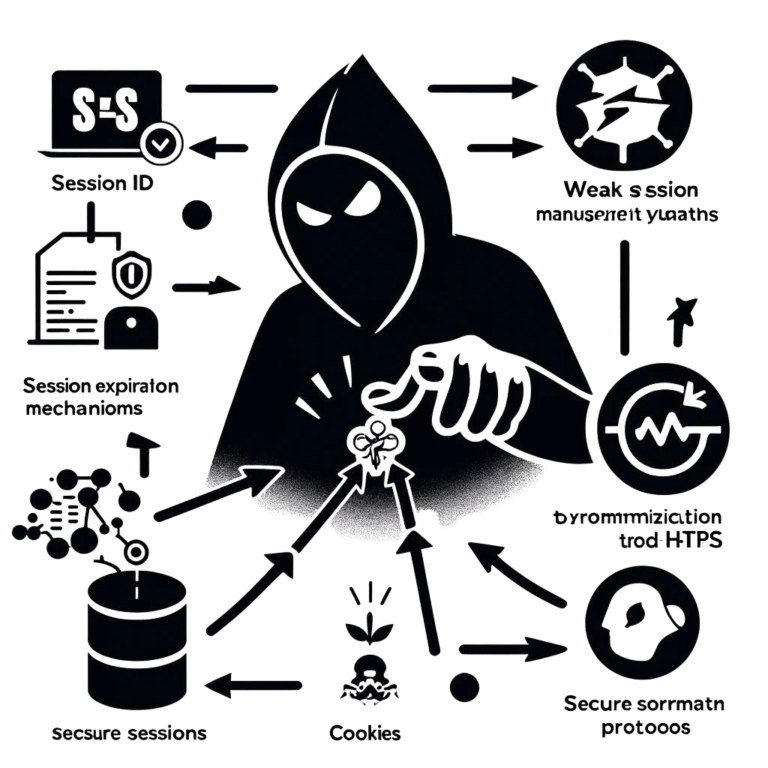
How to secure Web Apps from Session Management Vulnerabilities
Understanding Session Management Vulnerabilities Session management vulnerabilities in web applications pose a significant risk to the security…
-
Cross-Site Request Forgery (CSRF): What It Is and How to Stop It
Understanding CSRF Attacks Cross-Site Request Forgery, or CSRF for short, is a type of web vulnerability where…
-
The Dangers of Cross-Site Scripting: How to Secure Your Website
Understanding Cross-Site Scripting (XSS) Cross-Site Scripting (XSS) is a common security risk in web applications. It lets…
-
Essential Best Practices for Mobile App Security
The Importance of Mobile App Security Mobile applications have become a crucial part of our daily life,…
-
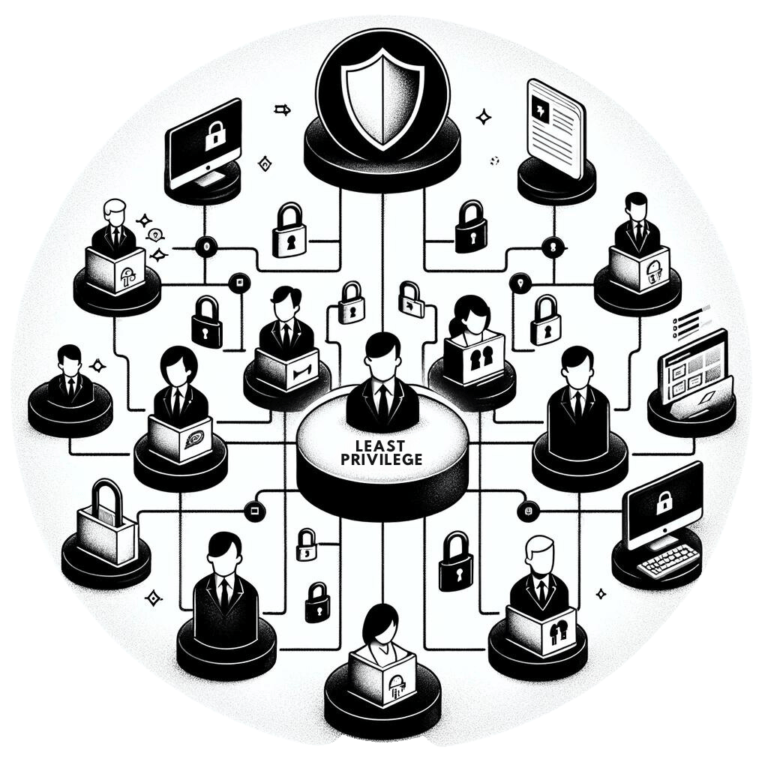
Mastering Principle of Least Privilege to Reduce Risk
Understanding the Principle of Least Privilege In cybersecurity, a key principle that organizations should follow is the…
-
Penetration Testing SOC 2 for Improved Security Compliance
Understanding Penetration Testing SOC 2 Certification What is Penetration Testing? In the world of online security, penetration…
-
Vulnerability vs Exploit: Understanding the Differences
Vulnerability vs Exploit? In cybersecurity, it’s important to know the difference between vulnerabilities and exploits to keep…
-
Protect Your Data: Essential SQL Injection Defense Strategies
What is SQL Injection? SQL Injection refers to a sort of online attack where hurtful computer codes…
-
Exploring Fuzzing: How Random Data Can Boost Your Cybersecurity
Introduction to Fuzzing in Cybersecurity Fuzzing (fuzz testing) is a cybersecurity technique that helps identify vulnerabilities in…
-
Mastering Nessus Vulnerability Scan Reports
Importance of Nessus Reports for Security Nessus vulnerability scan reports play a crucial role in enhancing the…
-
Common Vulnerabilities in Mobile Apps
Importance of Mobile App Security In today’s digital age, where mobile applications have become an integral part…
-
Web Application Penetration Testing Guide for Developers
Understanding Web Application Penetration Testing Checking a web application for security holes is important for developers to…
-
Use Desktop Application Pentesting to Enhance Business Security
Understanding Desktop Application Pentesting Desktop application penetration testing is a crucial aspect of securing your business applications…
-
Implementing Network Security Protocols for Improved Security
Understanding Network Security In today’s world of technology, it’s crucial to have strong security practices to keep…
-
Website Penetration Testing: Protect Your Business from Cyber Threats
Understanding Cyber Threats In today’s online world, businesses are at risk of cyber attacks that can harm…
-
Mastering Vulnerability Assessments: A Step-by-Step Guide
Understanding the Concept of Vulnerability Assessment In the world of cybersecurity, performing a vulnerability assessment is an…
-
Wireless Weaknesses: A Deep Dive into WiFi Penetration Testing
What is WiFi Penetration Testing WiFi penetration testing is a crucial aspect of assessing and strengthening the…
-
Master Penetration Testing: Secrets to Becoming a Cyber Ninja
Significance of Cybersecurity In the world of cybersecurity, it’s really important to have strong security measures in…
-
Beyond the Basics: Mastering IoT Penetration Testing
Introduction to IoT Penetration Testing Penetration testing is like giving your computer systems a security check-up. It…
-
Building Cyber Resilience: Evolving from Penetration Testing
Understanding Penetration Testing Penetration testing, also known as ethical hacking, is an important process in cybersecurity that…
-
Mastering Social Engineering: Penetration Testing for Human Networks
Introduction and Importance of Social Engineering Social engineering is a deceptive manipulation technique used by cyber attackers…
-
Mastering Cloud-Based Penetration Testing: Advanced Techniques
Introduction to Cloud-Based Penetration Testing In today’s digital landscape, the cloud has become an indispensable tool for…
-
Effective Penetration Testing Strategies for Mobile Applications
In today’s world, smartphones and tablets are a big part of our everyday life. We use them…
-
The Power of Penetration Testing
When it comes to penetration testing, understanding silent threats is crucial in identifying vulnerabilities that are hard…
-
Using Penetration Testing to Uncover New Cyber Threats
Penetration testing, also known as ethical hacking, is like a practice run for cyber attacks done by…