Mastering Physical Penetration Testing: An Insider’s Guide
When it comes to keeping your information safe online, it’s important to also consider physical security. Physical…

When it comes to keeping your information safe online, it’s important to also consider physical security. Physical…

Introduction Understanding Digital Assets and Their Importance Digital assets refer to any information or data that is…
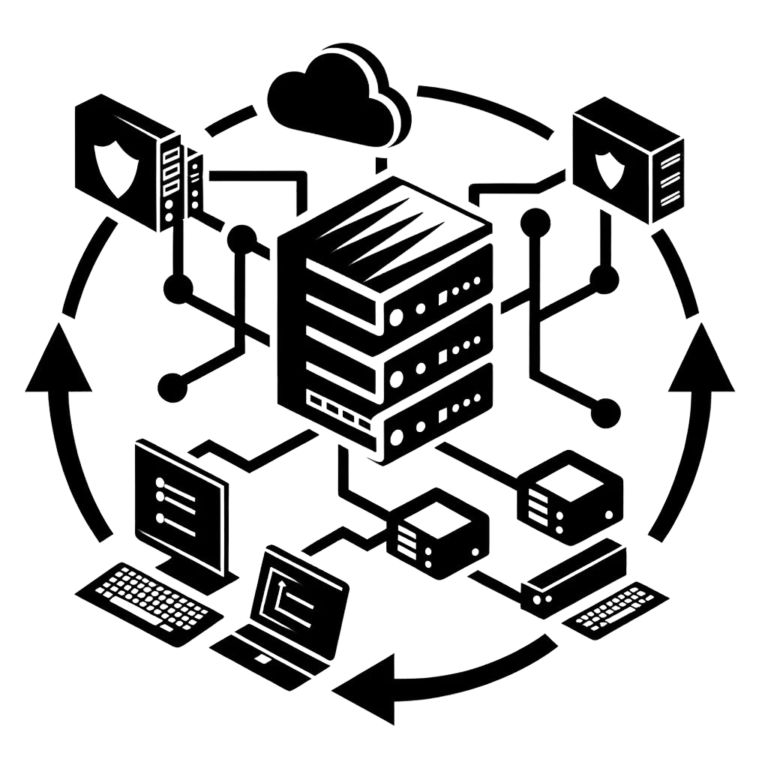
Understanding Network Penetration Testing Checking the strength of a network is really important in keeping an organization’s…

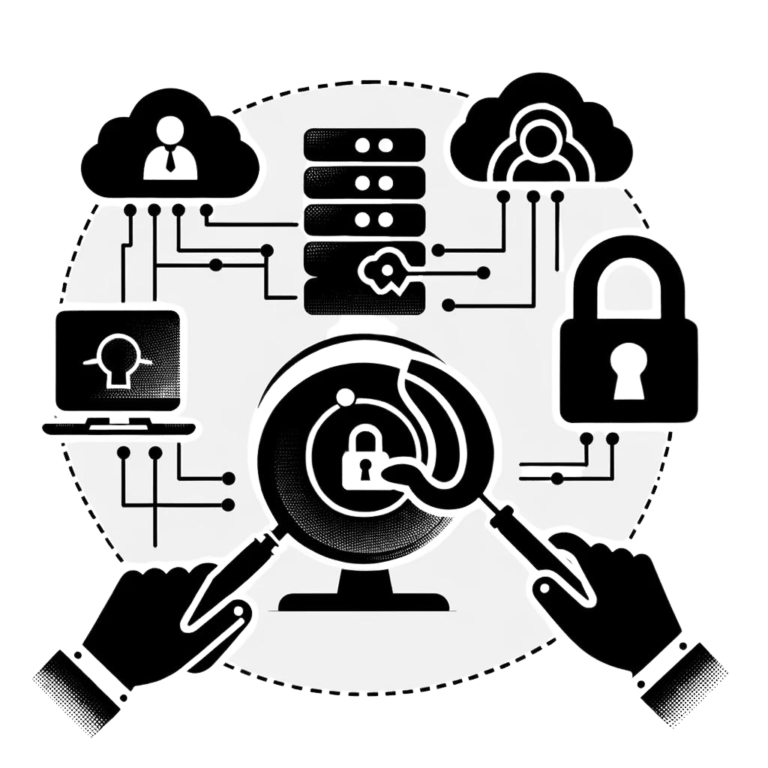
Introduction to Penetration Testing Understanding Penetration Testing Penetration testing, sometimes known as pen testing or ethical hacking,…
Understanding Cybersecurity When it comes to keeping your digital assets and personal information safe, understanding cybersecurity is…
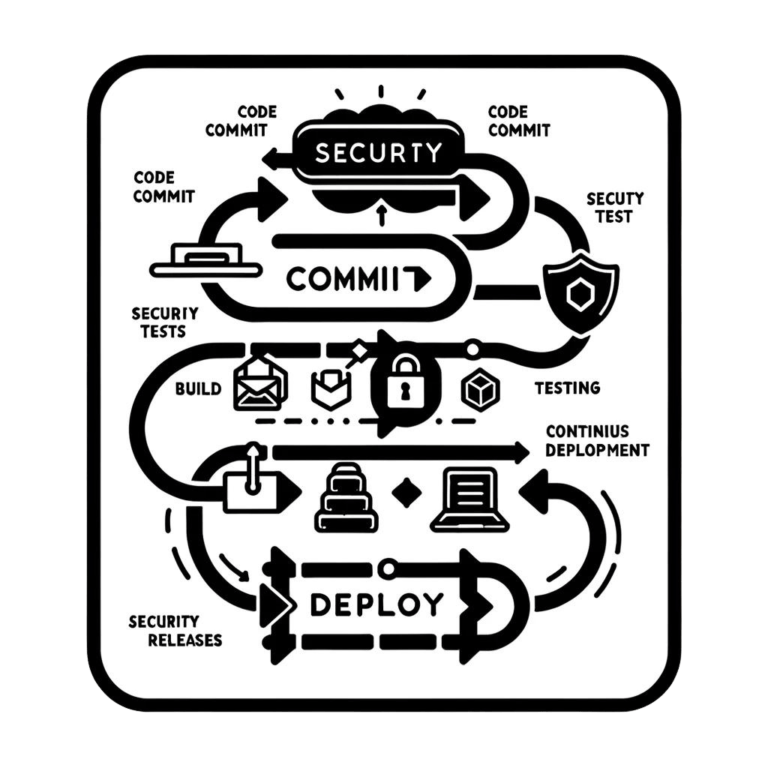
Introduction to Penetration Testing and Compliance Network penetration testing is an important part of cybersecurity because it…
The Importance of Cyber Security In today’s technologically advanced society, cyber security has become a crucial aspect…
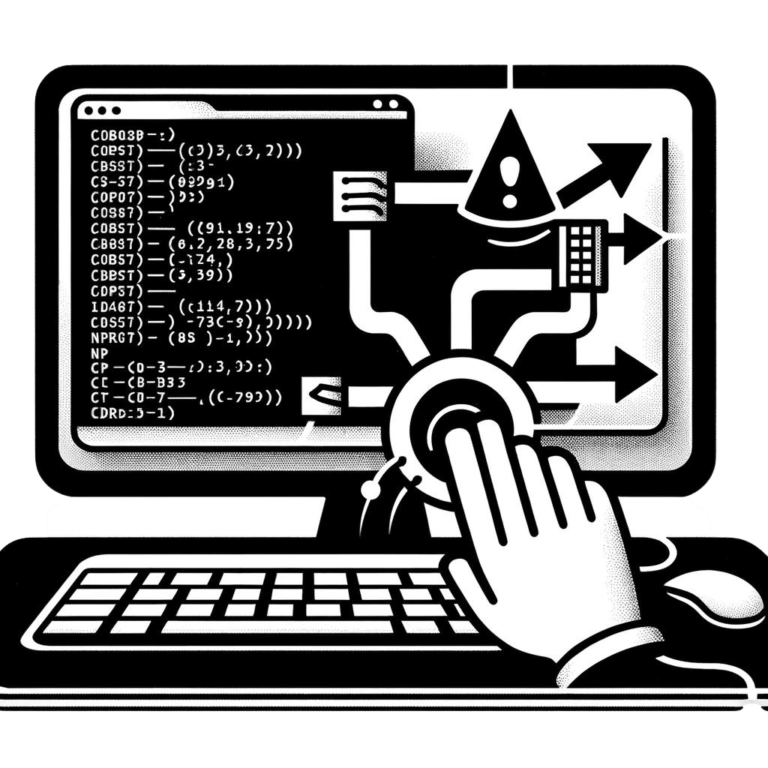
Pentesting, short for penetration testing, is a proactive approach to cybersecurity that involves simulating real-world attacks on…

Non-profit organizations work hard to do good things for society. But when it comes to keeping their…

In today’s digital world, there are more and more cyber threats that can harm our technology. This…